10 ENGLISH BOOKS RELATING TO «KEYLOGGER»
Discover the use of
keylogger in the following bibliographical selection. Books relating to
keylogger and brief extracts from same to provide context of its use in English literature.
1
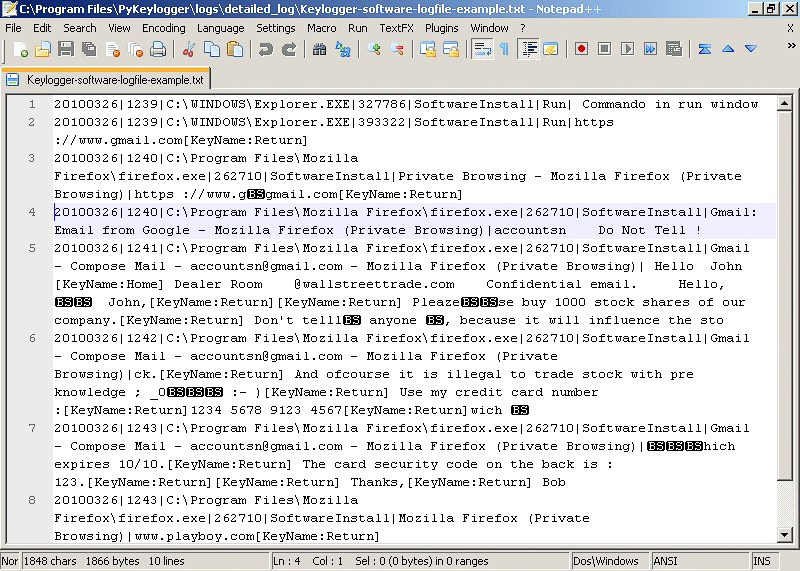
Ethical Hacking and Countermeasures: Attack Phases
41 notepadexe Untitled - Notepad I want to theckif this keylogger really works 1?:
2?:53 notepad.e>ce Untitled - Notepad looks like it works :P Monitoring Figure 5-
26 Revealer Keylogger is a keystroke logger. Tool: Revealer Keylogger ...
2
Recent Advances in Intrusion Detection: 13th International ...
In every other case, our detection system was able to detect the keylogger
correctly within a few seconds. Virtuoza Free Keylogger required a longer
window of observation to be detected. The Virtuoza Free Keylogger was indeed
the only ...
Somesh Jha, Robin Sommer, Christian Kreibich, 2010
3
Steal this Computer Book 4.0: What They Won't Tell You about ...
Actualkeylogger Creating a VB Keylogger Freekgbkeylogger-193 Freelogger
Homekeylogger.zip John-16w.zip Kbhook.zip Keylogger.zip Keylogger-king-free-
13 Kreview.zip Logger.zip (Mac OS X) Logkext.dmg (Mac OS X) Mkrack.dmg ...
4
Combating Spyware in the Enterprise
Instead, it simply blocks the processes that keyloggers use to have Windows
supply them with data. Keylogger Hunter installs very easily, following the
standard setup as most Windows-based applications. It places a shortcut to itself
in your ...
5
Security+ Guide to Network Security Fundamentals
Keyloggers A keylogger captures and stores each keystroke that a user types on
the computer's keyboard. This information can be later retrieved by the attacker or
secretly transmitted to a remote location. The attacker then searches for any ...
6
Combating Spyware in the Enterprise: Discover, Detect, and ...
Keylogger Hunter installs very easily, following the standard setup as most
Windows-based applications. It places a shortcut to itself in your Start menu, and
it gives you the option to launch the program immediately. Testing Keylogger
Hunter ...
There is a reason that Explorer . exe was the targeted process that KeyLogger .
DLL injected itself into. It was specifically chosen because it's the parent process
of all processes launched by the user. Therefore any user programs running ...
Larry Stevenson, Nancy Altholz, 2006
8
Advances in Computing and Communications, Part III: First ...
Another keylogger was implemented as a kernel mode rootkit (a device driver)
which remains hidden from the task manager and all such other applications e.g.
Process Explorer. We will refer to this as Sample B. We implemented this sample
...
Ajith Abraham, Jaime Lloret Mauri, John Buford, 2011
KEY LOGGER & SPYWARE A keylogger is something that records keystrokes
made on a computer. It captures every key pressed on the keyboard and stores it
down in a file or memory bank that can be viewed by the person performing the ...
10
Security Awareness: Applying Practical Security in Your World
Keylogger A keylogger silently captures and stores each keystroke that a user
types on the computer's keyboard. This information can be later retrieved by the
attacker or secretly transmitted to a remote location. The attacker then searches
for ...
10 NEWS ITEMS WHICH INCLUDE THE TERM «KEYLOGGER»
Find out what the national and international press are talking about and how the term
keylogger is used in the context of the following news items.
ZoneAlarm Launches Windows 10 Compatible Antivirus Software for …
... 2-way firewall, zero-day-attack protection, parental controls, Find My Laptop, PC tune-up, anti-keylogger, private browsing, and more. It is one ... «MarketWatch, Jul 15»
How to spot scams and protect your identity online
A keylogger is a type of spyware that records every tap you make on your keyboard and matches it to web pages you've visited. Adware installs ... «BT.com, Jul 15»
Global Industrial Cyber Security Market Report 2015
According to the report, the rise in cyber-attacks such as DDoS, keylogger, adware, and crimeware in the manufacturing and power sectors is ... «GlobeNewswire, Jul 15»
Operation Liberpy: Keyloggers and information theft in Latin America
A. It was a keylogger, a threat that undermines the security of a system by reporting all keyboard events (keys the user presses), as well as ... «We Live Security, Jul 15»
Hacking Team broke Bitcoin secrecy by targeting crucial wallet file
The company's embedded keylogger would surely capture the relevant password. And as one leaked company e-mail explained, the Money ... «Ars Technica, Jul 15»
UPDATE: Cracks show in testimony of ex-wife of former Vernon …
... two programs designed to permanently erase information from a computer as well as another program called a keylogger, that secretly saves ... «InfoTel News Ltd, Jul 15»
Don't be a victim of internet crime: How to spot scams and protect …
A keylogger is a type of spyware that records every tap you make on your keyboard and matches it to web pages you've visited. Adware installs ... «BT.com, Jul 15»
Hungary's Orbán government invests in spying technology for use …
RCS, or Galileo, is a very powerful surveillance software. It includes a keylogger function, which allows for intelligence agencies to track every ... «Hungarian Free Press, Jul 15»
PoSeidon: Inside the evolving world of point-of-sale malware
The initial infection vector has yet to be clearly identified, but Talos researchers suggest it could be the keylogger used in the malware. But without identifying ... «TechTarget, Jul 15»
FBI updates Most Wanted cyber felons list, offers US$4.2m bounties
The mastermind of the Zeus trojan; a car scamming screwball; an identity thief; a malvertiser, and a keylogger monger: nail these five net crims ... «The Register, Jul 15»