10 ENGLISH BOOKS RELATING TO «KEYLOGGING»
Discover the use of
keylogging in the following bibliographical selection. Books relating to
keylogging and brief extracts from same to provide context of its use in English literature.
4.4 Pseudocode for an event-monitoring keylogger This seems like a minor
variant of event copying, but it is worth noting because it is a mechanism for user
space keylogging on Microsoft Windows. Certain events, keyboard events among
...
2
Recent Advances in Intrusion Detection: 14th International ...
Malware considered for analysis and resulting PCC values Malware Label
Keylogging API API used PCC Backdoor.Win32.Poison.pg ✓ ✓ ∼1 Trojan-
Downloader.Win32.Zlob.vzd - - negligible Monitor.Win32.Perflogger.ca - -
negligible ...
Robin Sommer, Davide Balzarotti, Gregor Maier, 2011
3
Methods and Strategies of Process Research: Integrative ...
Copenhagen Business School, Denmark Although keylogging opens up many
possibilities for studying translation processes, the addition of eye tracking vastly
increases our ability to know what kind of process a translator engages in at any
...
Cecilia Alvstad, Adelina Hild, Elisabet Tiselius, 2011
4
CIW: Security Professional Study Guide: Exam 1D0-470
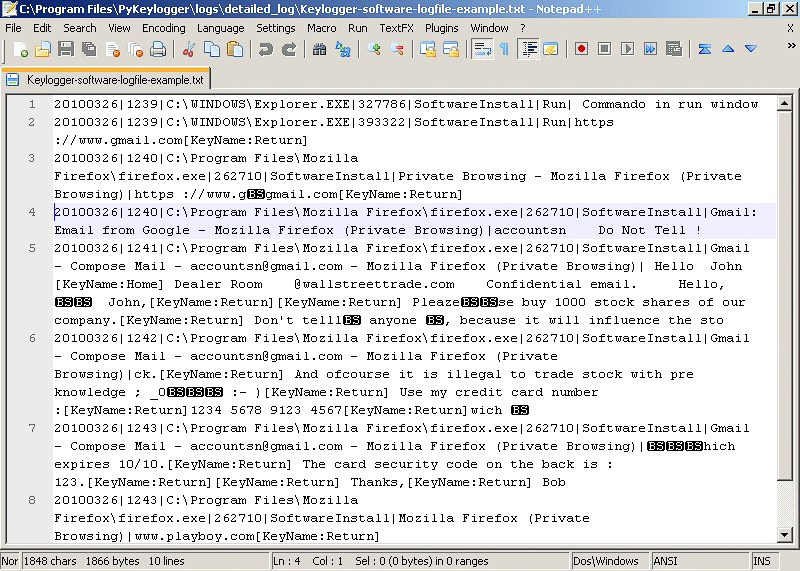
Keylogging. A keylogger invisibly records every keystroke on a computer, can
store the keystrokes in a file, and can optionally send the file to a predefined e-
mail address. A keylogger can: Intercept all keystrokes, mouse clicks, captions of
...
James Stanger, Patrick T. Lane, Tim Crothers, 2006
5
The New Forensics: Investigating Corporate Fraud and the ...
Dave's response was “Oh yeah, that'sjust like the virus keylogging tool Ijust read
about.” I wasn't sure what Dave was referring to, a not unusual predicament for
me when talking with him. The consulting world in which he specializes has him ...
6
Hypercrime: The New Geometry of Harm
The keylogging strategy, a more recent variant of access by duplication, captures
an identification key by acquiring data about how a keyboard is being used (most
obviously the passwords and pin numbers entered to accounts). This can be ...
7
Enhanced Discovering Computers
SeCure IT 7-1 Keyboard Monitoring Few programs have both criminal and
beneficial purposes, but keyboard monitoring software, also called keylogging
software, fits these objectives. This software runs undetected and stores every
keystroke ...
8
Wireless Mobile Internet Security
Keylogging is the action of tracking (or logging) the keys struck on a keyboard,
typically in a covert manner so that the person using the keyboard is unaware
that their actions are being monitored. There are numerous keylogging methods,
...
9
CCNP Security VPN 642-648 Official Cert Guide
Depending on the policy that has been applied to them at this stage, you can
check whether the connecting user is doing so from a virtual machine and for any
keylogging software that might have been intentionally or inadvertently installed
on ...
10
The Secure Online Business Handbook: A Practical Guide to ...
Keystroke logging (or keylogging) is a software method for capturing the user's
keystrokes. Writing keylogging programs is trivial and, like any computer program
, can be distributed as a Trojan or as a part of a virus or worm. The programs
often ...
10 NEWS ITEMS WHICH INCLUDE THE TERM «KEYLOGGING»
Find out what the national and international press are talking about and how the term
keylogging is used in the context of the following news items.
Benseron Offers Comodo Containment Solution For Retail POS
... technology to protect applications and data against unknown threats including remote takeover, keylogging, SSL sniffing, zero-day malware, ... «Point of Sale News, Jul 15»
Operation Liberpy Targets Latin America with Keylogging Malware
Operation Liberpy, an HTTP-based botnet for keylogging, has been stealing users' information since at least last August, managing to ... «Infosecurity Magazine, Jul 15»
Benseron To Implement Comodo Containment Technology To …
... technology to protect applications and data against unknown threats including remote takeover, keylogging, SSL sniffing, zero-day malware, ... «Virtual-Strategy Magazine, Jul 15»
Hacking Team Was Tracking Bitcoin Transactions Since January 2014
Hacking Team's Money Module operated by taking a victim's wallet.dat file, and together with the company's various keylogging systems, would ... «Softpedia News, Jul 15»
Smelling an mRAT: Defeating targeted attacks on enterprise mobiles
As they give administrative control of the device, they can enable keylogging, turn on video cameras and recording functions on mobiles, and ... «SC Magazine UK, Jul 15»
Mobile Malware Threats in 2015: Fraudsters Are Still Two Steps Ahead
The remainder are capable of performing malicious actions such as stealing personal information, sending SMS to premium numbers, keylogging and deploying ... «Security Intelligence, Jul 15»
What horrible things did we learn about Hacking Team today?
But UK cops kept flirting with Hacking Team, getting demos of keylogging spyware, and covertly monitoring wifi access points. Finally, Hacking ... «Boing Boing, Jul 15»
Seven steps on how to keep your passwords secure
This makes it impossible for keylogging software to record your login details, because all they see is a mouse click. Most banks now offer virtual ... «Economic Times, Jul 15»
A Windows Upgrade, And Virus Definitions
... and other sensitive information, and send it on to the source of the keylogging program. Many times keyloggers are used by corporations and ... «Island Eye News, Jul 15»
The Mob's IT Department
Someone called the police; a search turned up signal-jamming devices, keylogging software, and eavesdropping equipment. Investigators also ... «Bloomberg, Jul 15»